Researchers at the University of Rhode Island and Penn State University have been awarded a four-year, $1.5 million grant through the National Oceanic and Atmospheric Administration to study the effects of sea-level rise and how it may exacerbate the impact of extreme weather. The project will draw on expertise from researchers at URI’s Graduate School of Oceanography, its College of the Environment and Life Sciences, the Department of Ocean Engineering within the URI College of Engineering, and the URI Coastal Resources Center.
Other collaborative participants include the Schoodic Institute and the National Park Service. The overall goal of the project is to help communities, the National Park Service, and the U.S. Fish and Wildlife Service adapt and improve their resilience as the climate continues to change and extreme weather such as hurricanes and nor’easters continue to increase in terms of frequency and severity. 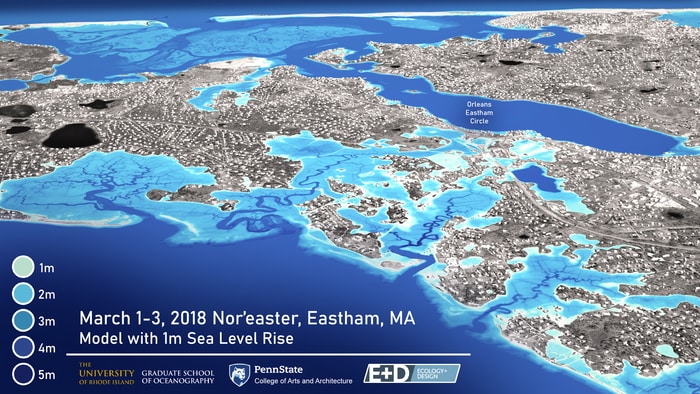
According to NOAA, the rate of sea-level rise is accelerating. Since 1993, the average global sea level has increased by 3.4 inches. By the end of the century, it is likely to rise at least one foot over 2000 levels. Sea level plays a role in flooding, shoreline erosion, and other hazards, affecting nearly 40 percent of the U.S. population living in high-population density coastal areas. However, despite what is known about sea-level rise, there is a lack of research available when it comes to how the impacts of nor’easters and hurricanes may be amplified as a result.
“There are a number of studies that have been done looking at just sea-level rise or just extreme weather, but what we’re really lacking in terms of clear understanding is the combined impact of these two phenomena,” said Isaac Ginis, professor of oceanography, who is leading the study. “This is especially important to us on the East Coast and in New England, where we’ve seen significant coastal flooding produced by waves and storm surge during nor’easters and hurricanes. How these effects are amplified by sea-level rise has been largely unexplored. This information gap inhibits our ability to properly plan for the future and is likely to lead to under-informed and ineffective adaptation measures.”
The project will expand the body of research related to the effects of extreme weather and sea-level rise on five New England national parks and two wildlife refuges – Cape Cod National Seashore, Boston Harbor Islands National Recreation Area, and New Bedford Whaling National Historical Park in Massachusetts; Ninigret National Wildlife Refuge, Trustom Pond National Wildlife Refuge, and Roger Williams National Memorial in Rhode Island; and Acadia National Park in Maine – as well as their surrounding communities.
The project was supported by all four members of Rhode Island’s congressional delegation and received letters of support from more than 15 local communities and local non-profits.
“This federal research funding will help URI faculty and students gather valuable information to answer questions about changing sea levels and in turn protect coastal communities from the effects of climate change,” said U.S. Senator Jack Reed.
Using state-of-the-art atmosphere, storm surge and wave/erosion supercomputer modeling the team will provide high-resolution recreations of the impact of the future storm and sea-level rise scenarios, identifying vulnerabilities in the ecosystems and infrastructure of the identified sites and their adjacent communities. The modeling will also include hazard, risk, and adaptability assessments, as well as mitigation scenarios.
“Rising seas and worsening storms driven by climate change are two major challenges Rhode Island will face in the decades to come,” said U.S. Senator Sheldon Whitehouse. “It’s fitting that the University of Rhode Island has been selected by NOAA to research ways to protect coastal areas from these dual threats.”
Researchers will work closely with the National Park Service, U.S. Fish and Wildlife Service, and stakeholders at the community level to tailor the research and translate the science in a way that can be incorporated into local resource management and adaptation measures to improve coastal resilience and to protect communities, people and infrastructure, and ecosystems.
“Each community has their own needs,” says Ginis, “but our modeling results will produce tailored and tangible information for local decision-makers – state and local governments, emergency management officials, town and city planners, and other stakeholders – to address their specific needs and enable them to plan and adapt as the sea level rises and the climate continues to change.”
Taking historical data into account as well as topography, geology, water depth, land elevation, natural processes such as shoreline changes, and human influence, the team will be able to project more than 50 years into the future, using 3-D visualization to provide computer simulations illustrating storm hazards and identifying potentially effective mitigation measures.
“As climate change continues to wreak havoc on communities across our state, it’s more important than ever to better understand the effects of rising sea levels and their impact during extreme weather events,” said Congressman Jim Langevin. “Devastating storms and flooding are becoming more frequent and severe, so we must invest in climate resiliency and adaption before it’s too late. I’m thrilled that the University of Rhode Island will now have the federal funding to lead the way on this critical area of research, and I look forward to reviewing the research.”
Ultimately, the project will open an important dialogue between researchers and local stakeholders, and Federal resource managers, and facilitate the development of practical and well-informed, science-based best practices that will guide future policies and resource management strategies to protect our coastal economy, environmental, cultural, and community resources.
“Climate change is one of the greatest challenges of our time, and we need to deal with this existential threat head-on,” said Congressman David Cicilline. “With the support of this federal grant, the University of Rhode Island and Penn State University will be able to study the impact climate-caused sea-level rise has on extreme weather. Their project will ultimately provide our coastal communities with the information they need to improve resiliency and plan for rising sea levels and severe weather events.”
 How to resolve AdBlock issue?
How to resolve AdBlock issue?